Security teams rarely struggle with a lack of tools. Most already have SIEM, endpoint protection, threat intelligence feeds, and more. The problem usually shows up somewhere else. Alerts come in faster than teams can handle them. Analysts jump between systems trying to piece together context. Decisions take longer than they should.
That gap between detection and action is where most security programs feel slow. This is exactly where SOAR (Security, Orchestration, Automation, and Response) integration is supposed to help. But calling it the “missing link” is only partly true. It depends on what is actually broken in your environment.
What SOAR Integration Actually Does

Before deciding if SOAR is the missing piece, it helps to be clear about what it really does. At its core, it connects your existing tools and automates how they work together.
Instead of treating alerts as isolated events, SOAR platforms pull data from multiple systems, enrich it, and trigger predefined actions. That includes things like isolating a device, blocking an IP, or opening a ticket.
According to IBM’s overview, these platforms reduce mean time to detect and respond by coordinating tools and automating workflows.
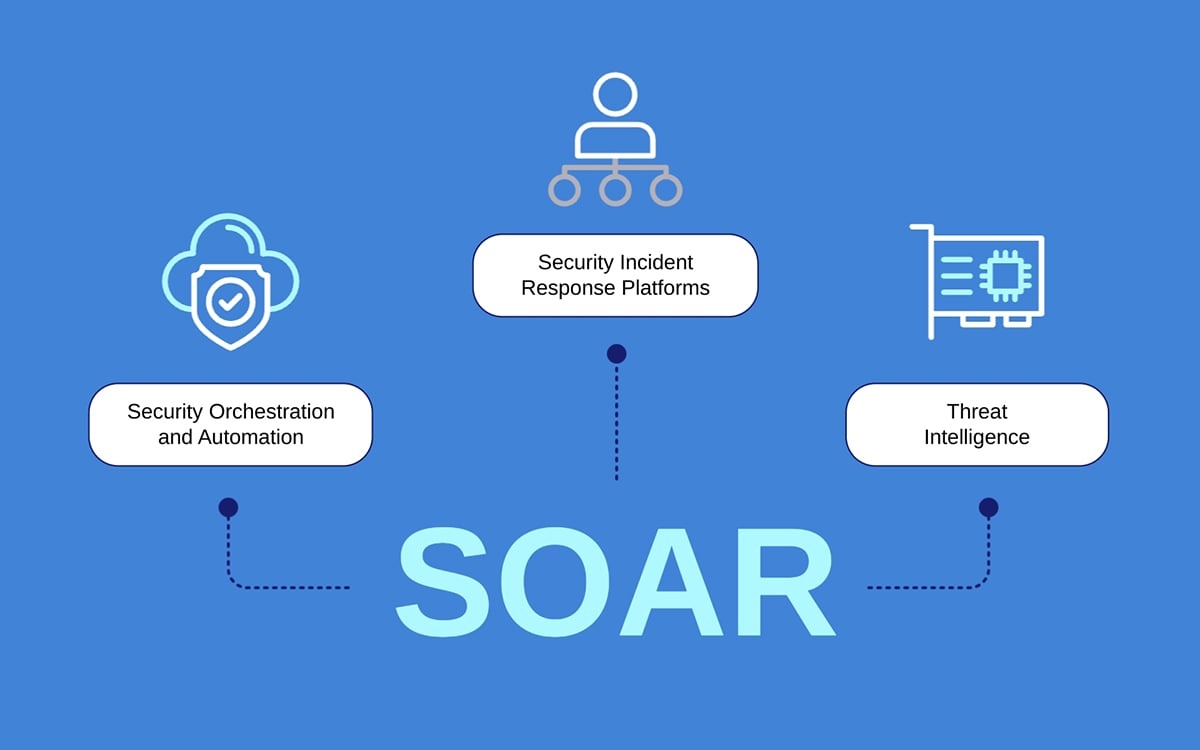
SOAR combines orchestration, automation, and response into a single workflow system that connects tools and standardizes actions.
That sounds simple, but in practice, the value depends on how well your current tools already work together.
Where a SOAR Provider Fits Into the Stack
When teams start evaluating a SOAR provider, they often expect it to replace complexity. In reality, it sits on top of existing systems and tries to organize them. DarkOwl explains that SOAR is not a standalone defense layer. It depends on integrations with SIEM, EDR, and threat intelligence to function properly.
That matters because if those underlying tools are inconsistent, SOAR will inherit that inconsistency. It does not fix weak data or unclear workflows. It just automates whatever is already there.
So the real question is not “Do you need SOAR?” but “Is your current process stable enough to automate?”
The Real Problem: Fragmentation, Not Detection

Most modern security stacks already detect threats well enough. The issue is what happens after detection.
Teams deal with:
- Too many alerts with little context
- Manual triage across multiple systems
- Repetitive investigation steps
- Delays between identifying and responding to incidents
ResearchGate study shows that security operations centers are often overwhelmed by alert volume, leading to delayed responses and increased risk.
This is where SOAR helps. It reduces manual steps and standardizes response workflows. By automating enrichment and triage, it shortens the path from alert to action.
But again, this only works if the alerts themselves are meaningful.
What You Actually Gain From SOAR Integration
If implemented well, SOAR changes how work gets done rather than what tools you use.
Studies consistently show improvements in response speed. For example, a 2025 analysis of automated incident management found that SOAR reduced response time and minimized human error in security operations (CEUR Workshop Proceedings, 2025).
JDACM study on incident containment, 2025 shows containment times dropping from hours to minutes when workflows are automated.
Here is a simple way to think about the shift:
| Before SOAR | After SOAR |
| Analysts manually collect context | Context is automatically enriched |
| Alerts handled one by one | Alerts processed through workflows |
| Response depends on individual judgment | Response follows standardized playbooks |
| Time to respond varies widely | Time to respond becomes predictable |
The main benefit is consistency. Speed improves as a result, but consistency is what actually makes operations scalable.
Where SOAR Integration Falls Short
It is easy to assume automation will fix operational issues. In practice, it can expose them instead.
Some common problems show up quickly:
- Playbooks become outdated as threats evolve
- Integrations break or require constant maintenance
- Poor-quality alerts get automated instead of filtered
- Teams rely too much on predefined logic
According to recent analysis of SOAR limitations, rigid playbooks and weak integrations can actually slow teams down instead of helping them.
There is also the issue of setup time. Implementing SOAR can take months, especially in complex environments. During that time, teams are still handling incidents manually.
So while it promises efficiency, it also introduces overhead. Whether that trade-off is worth it depends on how mature your processes already are.
A Practical Way to Decide If You Need SOAR
Instead of starting with the tool, start with your workflow.
Ask a few direct questions:
- Are analysts repeating the same investigation steps daily?
- Do multiple tools need to be checked for every alert?
- Is response time inconsistent across similar incidents?
- Are decisions dependent on specific individuals?
If the answer to most of these is yes, SOAR can help.
If not, adding SOAR may just add complexity.
It is also useful to think in stages:
- Early stage: Focus on improving detection quality
- Mid stage: Standardize workflows manually
- Mature stage: Automate those workflows with SOAR
Skipping the middle step is where many implementations fail.
The Role of Automation in Modern Security Operations

Automation is not optional anymore. The volume of alerts makes manual handling unrealistic.
Some estimates suggest that advanced SOAR implementations can reduce incident response time by up to 70 percent, especially when combined with AI-driven prioritization (TrustCloud AI study, 2025).
But automation should not replace human judgment entirely. It should handle routine decisions and leave complex cases to analysts.
The goal is not to remove people from the process. It is to reduce the amount of low-value work they have to do.
That distinction matters. Automation done well increases clarity. Automation done poorly just increases noise.
So, Is SOAR the Missing Link?
Sometimes it is. Often it is not.
SOAR works best when the main issue is coordination between tools and consistency in response. In that case, it acts as a layer that ties everything together and removes friction from daily operations.
But if the problem is unclear processes, poor data quality, or too many false positives, SOAR will not fix that. It will just automate the problem.
A better way to frame it is this: SOAR is not the missing link in every security stack. It is the right next step for teams that already know how they want to respond and need to do it faster and more consistently.